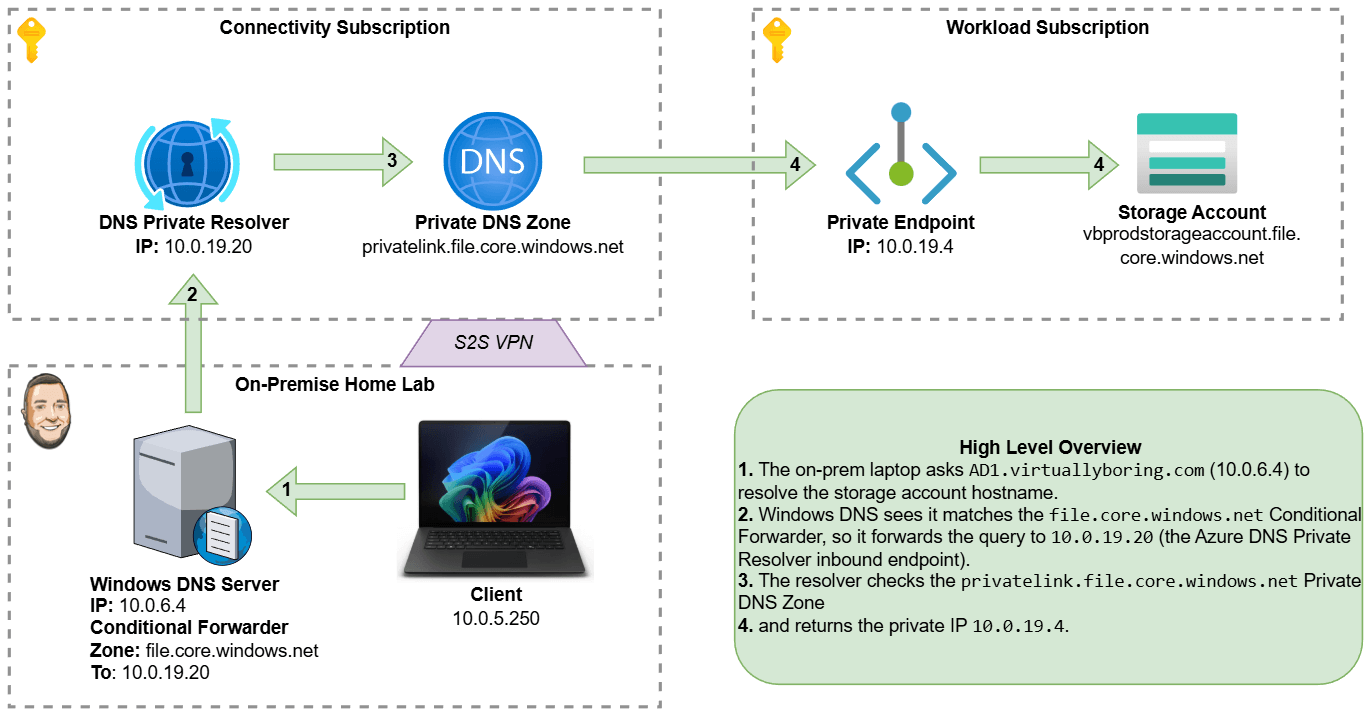
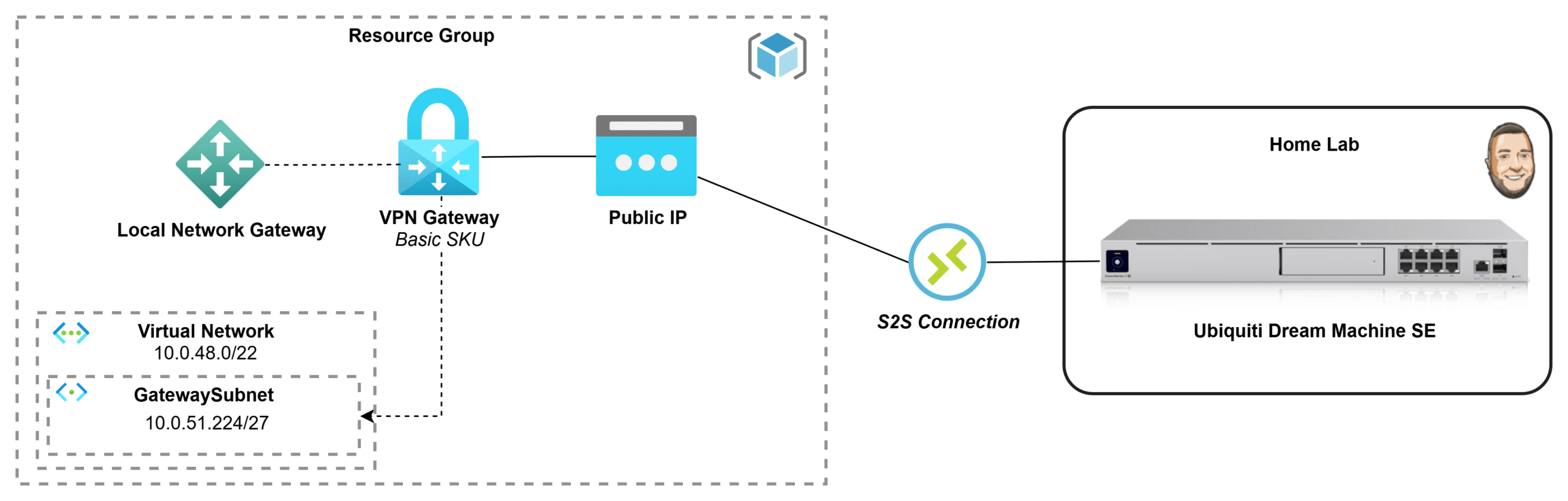
If you’ve got an Azure subscription through Visual Studio Enterprise, you’ve basically been handed the perfect playground for testing and learning in the cloud. But once you start building resources inside a private Azure network, you quickly hit the next challenge: how do you securely connect it back to your home lab without exposing everything to the internet? In this post, I’m going to go through the process of how I deployed a Basic Azure Virtual Network Gateway and connected it to my Ubiquiti Dream Machine, creating a secure site-to-site VPN tunnel between my Azure VNet and my home network. I wanted to document what that process looked like for me and share it in case it helps someone else doing the same thing.
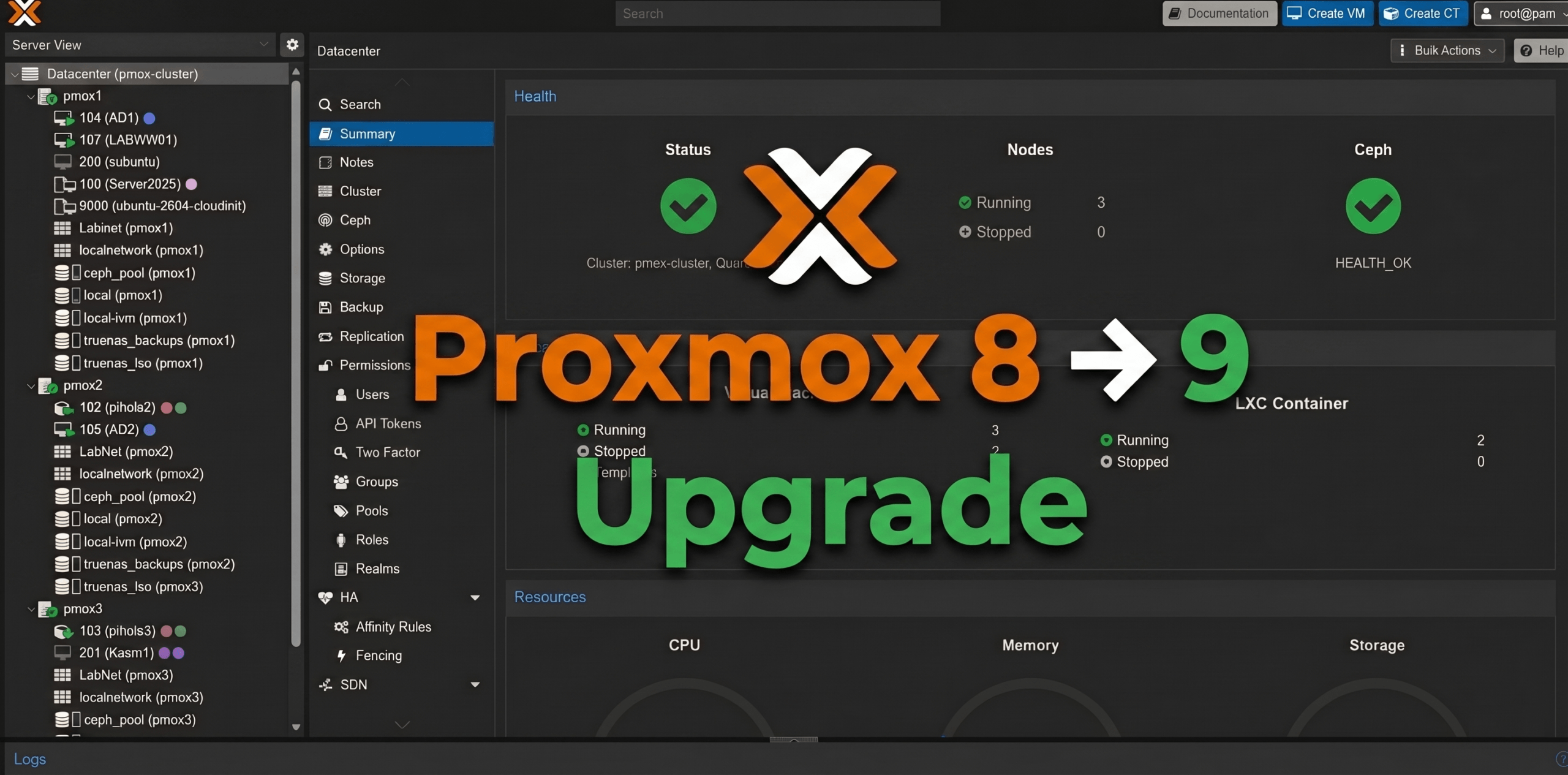
Upgrading Proxmox VE 8 to 9: A Real-World Walkthrough
I’ll be honest — I’ve been putting this off for a while. Proxmox VE 9 dropped earlier this year, and every time I looked at the upgrade guide I thought “yeah, I’ll get to that.” This weekend I finally ran out of excuses and carved out some time to tackle it. Three nodes, a hyper-converged Ceph cluster, and a handful of HA-managed VMs. Nothing exotic, but enough moving parts to make it interesting. This post is meant to complement the official Proxmox upgrade documentation — not replace it. If you want the authoritative source, go there. What I’m documenting here is what the upgrade actually looked like in practice on a real homelab cluster, including the things pve8to9 flagged and how I resolved them. Why Upgrade to Proxmox VE 9? Before we get into the how, it’s worth covering the why. Proxmox VE 8 remains functional and receives security updates, but PVE 9 brings meaningful improvements across storage, networking, HA, and container management that make the upgrade worth doing — especially if you’re running any production-adjacent workloads. Debian 13 “Trixie” Foundation PVE 9.0 is built on Debian 13 “Trixie”, bringing a newer kernel (6.14.x in 9.0, jumping to 7.0 in 9.2), updated toolchains, and broader hardware support. QEMU jumps from 8.x to 10.x/11.x, LXC to 6.0.4, and ZFS to 2.3.3. If you’re running newer hardware …